System-Level Security for IoT-Enabled e-Health Systems
The evolution of e-health systems with increased connectivity through the advancement of the Internet of Things (IoT) has exposed them to a new frontier of cybersecurity vulnerabilities from which they were previously shielded.
The Problem
Healthcare providers today depend on nearly 100 million connected medical devices to deliver cost-effective and lifesaving treatment to patients, and the number of these connected devices is expected to double in the next 2–3 years. This new connectivity exposes critical healthcare systems to cybersecurity threats they were previously shielded from.
The Solution
The initial research successfully sustained a $2 million research contract with multiple industry and government partners to investigate and develop solutions and policies for securing IoT-enabled e-health systems. Media coverage included Carleton University newsroom, CityNews Ottawa, and Evamax.
2
Publications
$2M+
Project Value
3
Government Partners
3
Media Outlet Coverage
Why It's Hard
The primary goal of this work is to develop a comprehensive system-level security platform, capable of guaranteeing acceptable levels of security, privacy, and trust in a heterogeneous IoT-enabled e-health system. Using threat modeling (OWASP Threat Dragon), risk analysis, and enterprise system analysis, security deficiencies in cloud-based IoT platforms were surveyed and documented in partnership with Defence Research and Development Canada's Centre for Security Science, National Research Council, and Public Safety Canada.
The Process
Discovery
Threat Landscape Survey
Surveyed and documented security deficiencies in cloud-based IoT platforms used in healthcare in partnership with DRDC, NRC, and Public Safety Canada.
Threat surveyVulnerability catalogArchitecture
Security Platform Design
Used threat modeling (OWASP Threat Dragon), risk analysis, and enterprise system analysis to design a comprehensive system-level security platform.
Threat modelRisk registerSecurity architectureShip
Research Contract & Media
Successfully initiated a $2M research contract with multiple industry and government partners; project received broad media coverage.
Research contractMedia coverage
Architecture
IoT Devices
Medical Sensors & Devices
Cloud Platform
e-Health Data Infrastructure
Security Layer
Threat Modeling & Risk Analysis
Policy Framework
Government & Industry Partners
IoT Devices
Medical Sensors & Devices
Cloud Platform
e-Health Data Infrastructure
Security Layer
Threat Modeling & Risk Analysis
Policy Framework
Government & Industry Partners
How It Works
Map the System
Identify all IoT devices, cloud connections, and data flows across the heterogeneous e-health system.
Model Threats
Apply OWASP Threat Dragon to systematically identify, categorize, and prioritize threats at every system boundary.
Develop Protections
Translate prioritized risks into security controls, policies, and architectural recommendations for the full system.
Figures
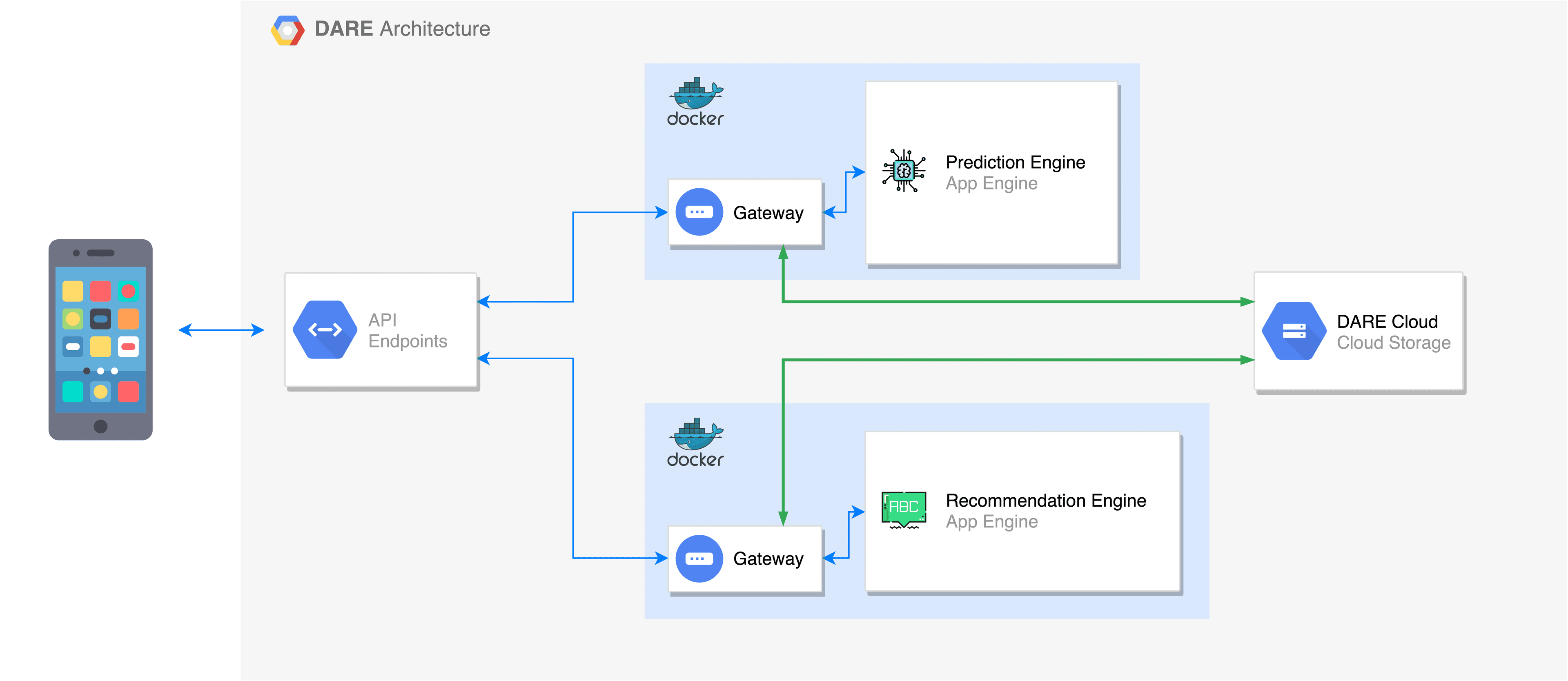
DARE framework architecture
Techniques
- ✓Threat Modeling
- ✓Risk Analysis
- ✓Risk Prioritization
- ✓Enterprise System Analysis
Technologies
- ✓OWASP Threat Dragon
- ✓IoT Security