RESEARCH
Leveraging External Data Sources to Enhance Secure System Design
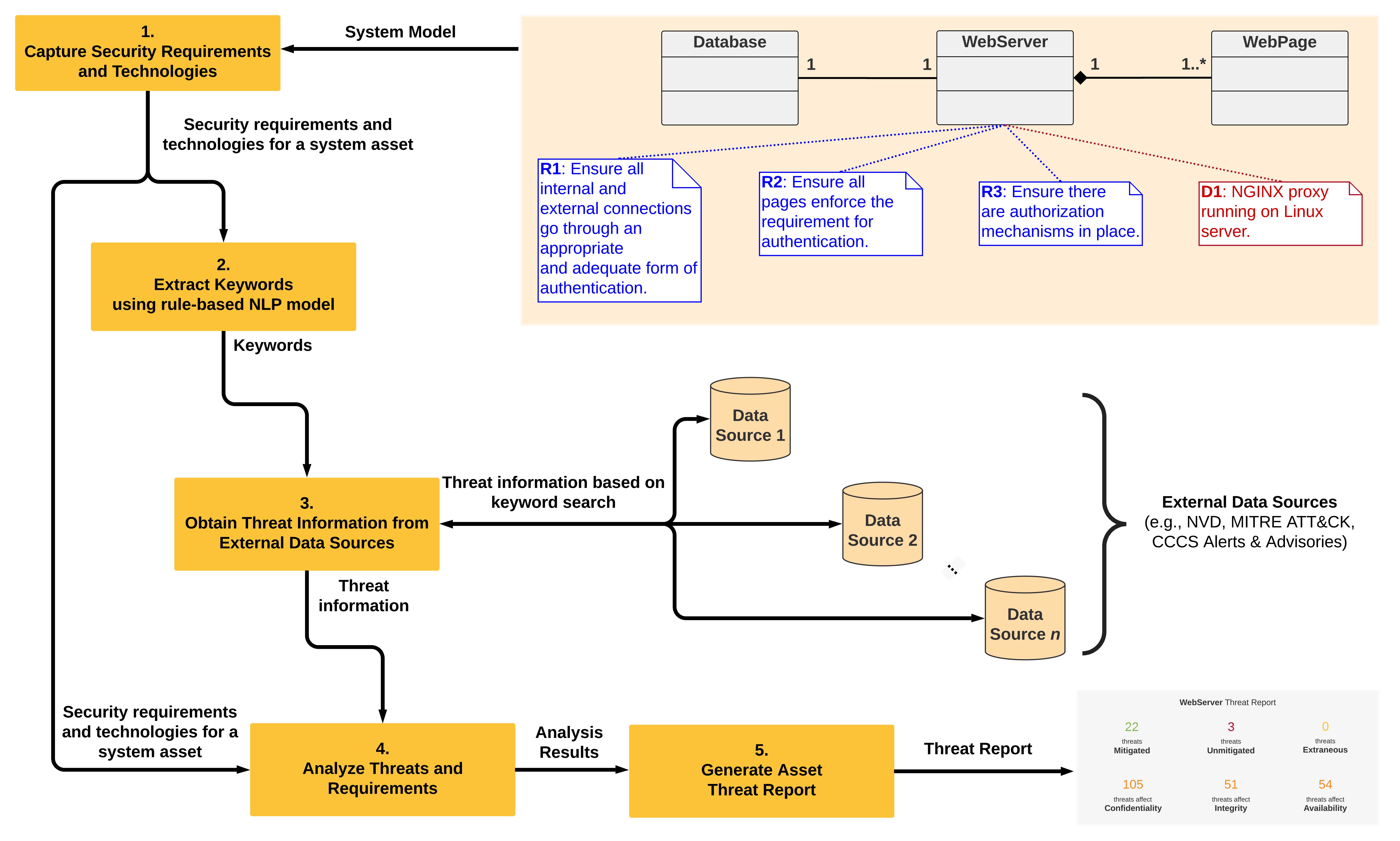
Today's software systems are riddled with security vulnerabilities that invite attack. We envisage a secure software design process at the architectural level, in which the security requirements are adequate, thus enabling appropriate security controls to be implemented to mitigate known threats and vulnerabilities. How can we ensure that the security requirements are adequate? In this paper, we tackle this question by focusing on how external online data sources for vulnerabilities, attack patterns, threat intelligence, and other security information can be leveraged, using Natural Language Processing (NLP), to produce a report to assist designers in validating the adequacy of the security requirements. This validation is done by determining which requirements map to known threats (identified from the external data), which requirements may be extraneous, and which threats may need a closer look in order to identify new requirements. We first describe the availability and nature of the external data, followed by how we employ NLP to process the data and produce the report. We include an illustrative example of our approach.
Key Takeaways
01. Context
Software systems today are riddled with vulnerabilities that invite exploitation by attackers. To reinforce this statement, consider, for instance, the Verizon 2020 Data Breach Investigations Report which indicates that web applications were involved in 43% of 3,950 data breaches worldwide. Further, the top hacking methods used in retail industry breaches were 45% stolen credentials, 40% vulnerability exploits, and 15% brute force. The prevalence of security vulnerabilities in modern software systems makes the task of developing secure software especially challenging.
02. Problem
A common challenge is the rush to market that commercial development teams face, leaving very little time to design software that is secure as well as functional. Another challenge is that the average development team lacks the know-how and the tools to create secure software. A third challenge is that there has not been sufficient motivation for developers to produce secure software. If an application fails due to a security flaw, the application's vendor is not subject to legal penalties, unlike the construction company for a bridge that collapses due to a mechanical design flaw.
03. Solution
In this work, we tackle the above challenge of lack of security know-how and tools by supporting the design process with an approach for ensuring that security requirements are adequate, i.e. the requirements will lead to security controls that mitigate known threats and vulnerabilities. Having an adequate set of requirements can help designers in building systems that have appropriate controls capable of mitigating the threats that actually affect the system components. We leverage available online external data, such as databases of vulnerabilities, threats, and attack patterns, to assist designers in validating the adequacy of their security requirements.
04. Impact
The output of our approach is a report that supports the architecture design phase of the software development lifecycle (SDLC) in terms of security evaluation and assurance activities, by assisting designers in ensuring that there are adequate requirements to mitigate known threats based on their design decisions. An important benefit of our approach is that it is carried out at the architecture design stage early in the SDLC, when it is less costly to make changes, and when the negative impacts of poor design decisions that become multiplied at the code level can be avoided.
